How SPOT Works¶
SPOT is an email-security tool that decides whether each incoming message is a phishing or business-email-compromise attempt, and helps the operator act on that decision. This page explains how an email moves through SPOT, what each stage does, and what the operator ultimately sees.
The journey of one email¶
Every email handled by SPOT goes through the same five stages, regardless of how it arrived or how strict the chosen policy is.
flowchart LR
Mail([Mail server])
Retriever[Mail retriever]
Enrich[Enrichment]
KB[(Knowledge store)]
Workflow[Workflow]
Analyzer1[Analyzer]
Analyzer2[Analyzer]
Verdict{{Verdict}}
Action[Action: tag /<br/>quarantine / allow]
Dashboard[Dashboard]
Mail -->|new email| Retriever
Retriever -->|ingest| Enrich
Enrich -.->|read context| KB
Enrich --> Workflow
Workflow --> Analyzer1
Workflow --> Analyzer2
Analyzer1 --> Verdict
Analyzer2 --> Verdict
Verdict --> Action
Verdict --> Dashboard1. Ingestion¶
An email enters SPOT through a mail retriever. A retriever is a small adapter that lives between the mail server and SPOT: it watches for new messages and hands each one to SPOT in a consistent shape, no matter where the message came from. Some retrievers sit inline on the SMTP path (so they can hold or tag a message before it reaches the inbox); others poll a mailbox after delivery. From SPOT's point of view, both styles look the same.
2. Enrichment¶
Before any classifier looks at the email, SPOT enriches it with organisational context. Context providers publish facts that the analyzers can consult ; who the company's executives are, which domains belong to known partners, what the policy book says about wire transfers, and so on. Each provider keeps its facts up to date on its own schedule and deposits them into a shared knowledge store.
Enrichment is what lets SPOT tell the difference between a stranger emailing the CFO out of the blue and a finance partner who has been corresponding with the company for months. It is also what makes a generic phishing detector aware of the specific organisation it is defending.
3. Analysis¶
Each email is then handed to a workflow ; an ordered set of stages that decides which analyzers should look at the message and how their answers should combine. An analyzer is a single classifier with an opinion: a language-model analyzer reads the prose, a rule-based analyzer flags known patterns, an ML analyzer looks at structural features, a threat-intelligence analyzer compares URLs and senders to known-bad lists. Each analyzer returns a verdict and a confidence score; the workflow merges those into a single platform verdict.
4. Verdict & action¶
The platform produces one verdict per email: a phishing decision (yes / no), a threat level (none / low / medium / high / critical), a confidence score, the indicators that drove the decision, and a recommended action (allow, flag, review, quarantine). When SPOT is running inline, the recommended action is applied straight away ; for example, by tagging the message with a header for downstream filtering or returning a temporary-failure to the sending server. When SPOT is running out-of-band, the verdict simply lands in the dashboard for human review.
5. Review¶
Every analysed email and its verdict is recorded so an operator can look at it later. The dashboard is the place where operators spend most of their time: searching emails, opening an analysis to see which analyzers said what, comparing related messages, and adjusting workflows when the policy needs to change.
What an operator sees¶
The operator's view of SPOT is the dashboard. There are five places they typically work in:
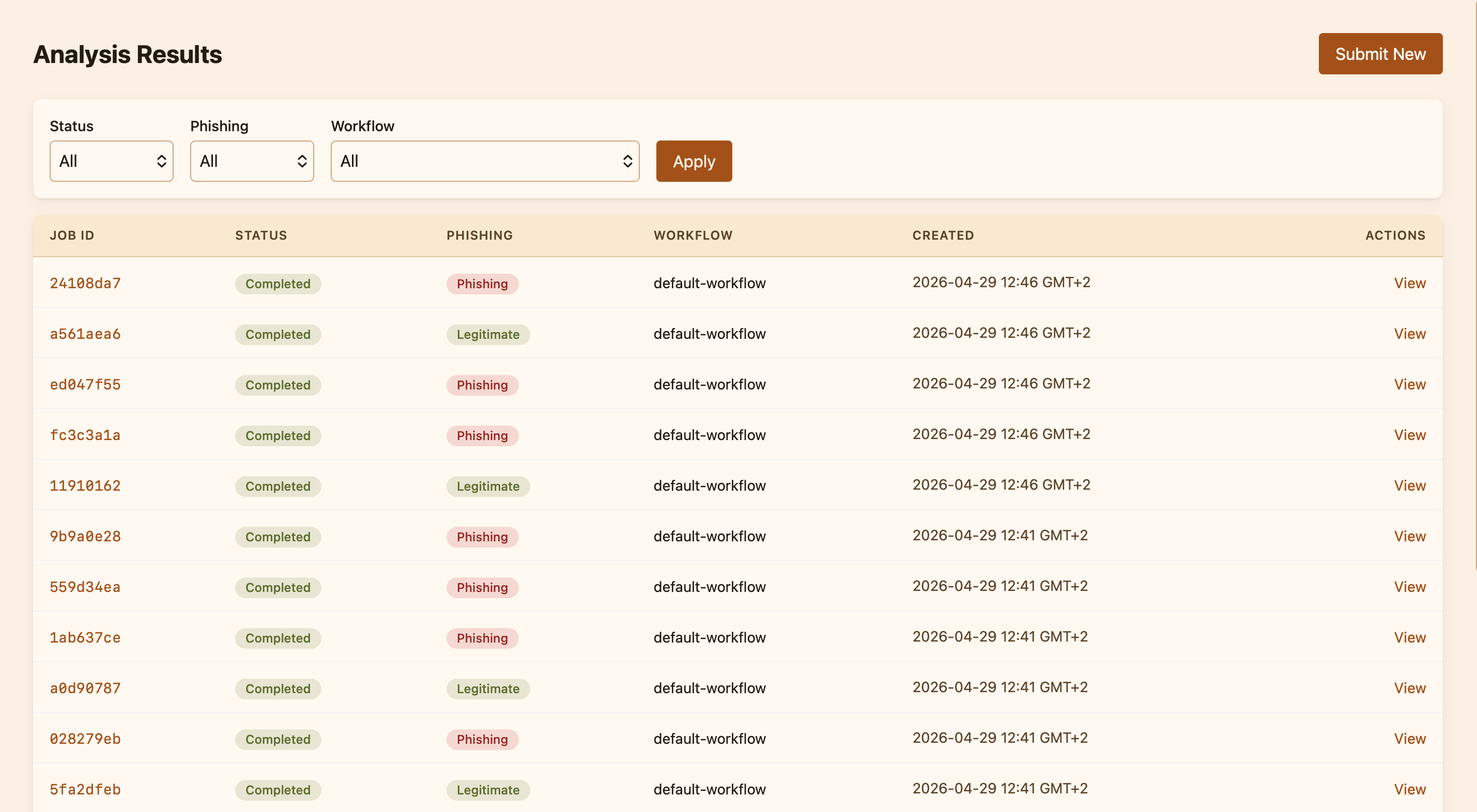
Analyses ; the live and historical list of every classification SPOT has produced. Each row is one email, with its verdict, threat level, and the workflow that produced it.
Emails ; the original messages, stored encrypted and viewable on demand. Useful for incident response: "show me everything from this sender in the last week."
Workflows ; the set of policies that decide which analyzers run and how strictly. The dashboard ships with a default workflow and lets operators clone, edit, or replace it.
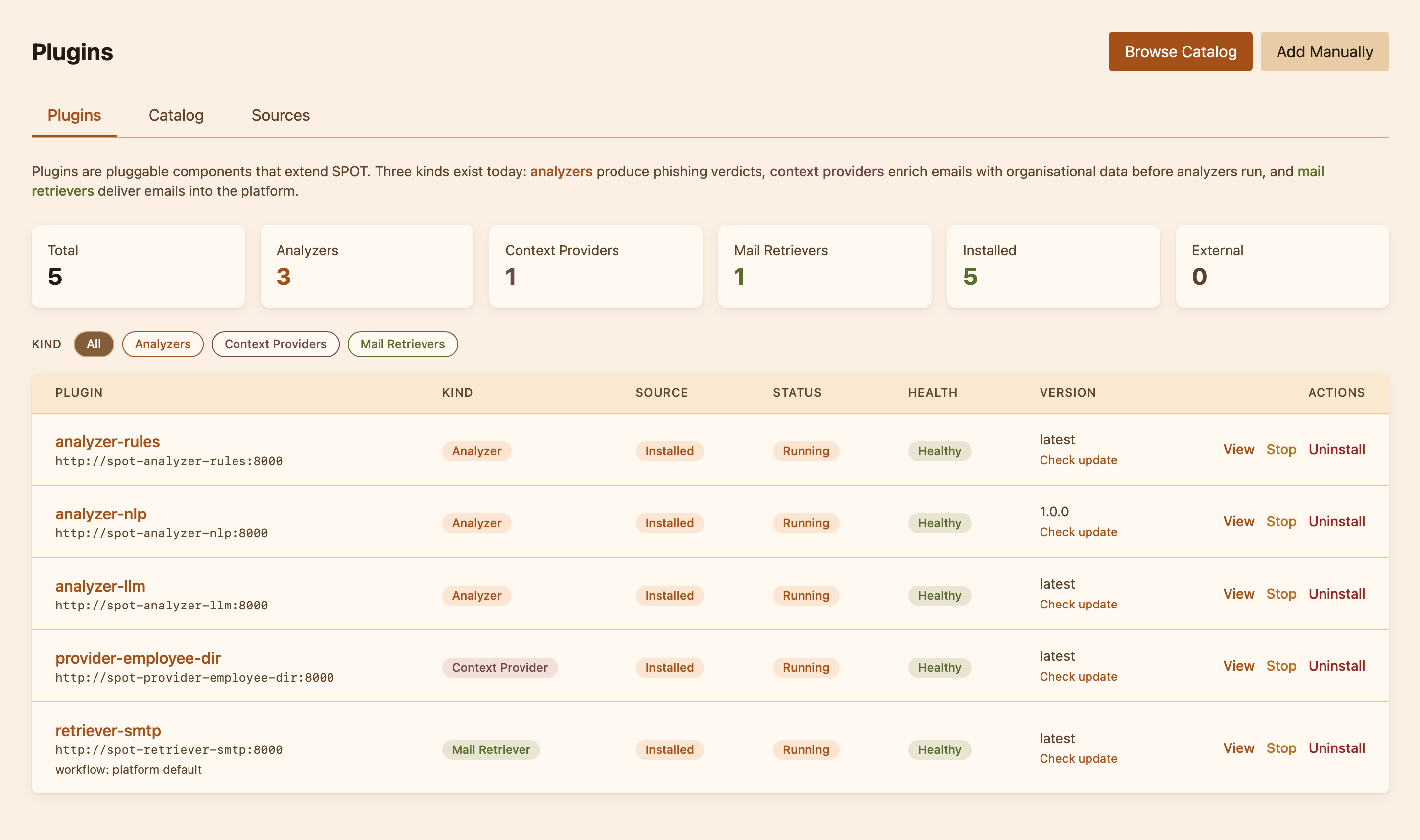
Plugins ; the catalog of available plugins (analyzers, context providers, mail retrievers) and the list of what is currently installed and running. This is where operators add a new analyzer or register a new context provider.
Knowledge ; the consolidated body of organisational facts that context providers have deposited. Operators can browse it, search by tag, or query it the way an analyzer would.
Why the pieces are split this way¶
SPOT is built around the idea that the questions "where does the email come from?", "what does my organisation know about it?", and "is it a phish?" are independent. A retriever does not need to understand language; an analyzer does not need to know how mail is delivered; a context provider does not need to know what the workflow is going to do with its data. Keeping them separate means the operator can swap any one piece without touching the others ; install a different language model, plug in a new threat-intel feed, switch the mail integration ; and SPOT keeps working.